Signal Engine Start 619-354-4038 Unlocking Verified Caller Lookup

Signal Engine Start 619-354-4038 introduces a cryptographically anchored approach to verified caller lookup, emphasizing real-time provenance and low-latency signaling. The system aligns input with a lightweight processing core to execute rapid signature matching, endpoint queries, and succinct identifiers with confidence scores. It prioritizes transparency, auditable workflows, and secure telemetry, while enforcing data minimization and granular consent. The framework promises reproducible protections and disciplined governance, but unanswered questions remain about operational boundaries and practical implications.
What Is Verified Caller Lookup and Why It Matters
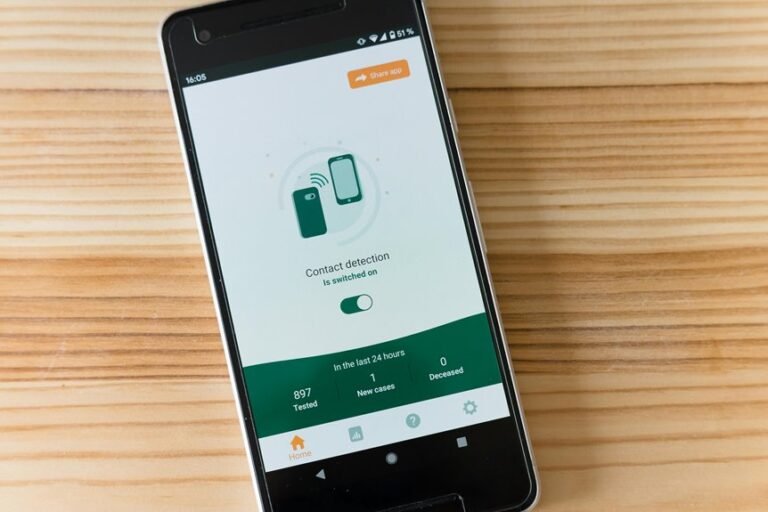
Verified Caller Lookup refers to a verification process that confirms the identity and legitimacy of a telephone caller, typically by cross-referencing caller information with trusted databases and cryptographic attestations.
The mechanism establishes verified lookup as a foundational capability, enabling systems to assess provenance and reduce impersonation risk.
This framework strengthens caller trust by providing auditable, cryptographically anchored identity signals for each interaction.
How Signal Engine Start 619-354-4038 Works in Real Time
How does Signal Engine start 619-354-4038 operate in real time to deliver verified caller information? The system synchronizes signal input with a lightweight processing core, performing rapid signature matching and endpoint querying. Engine start two word; Verified caller, lookup trust two word. Real-time latency remains under threshold, delivering succinct identifiers and confidence scores, while only essential telemetry traverses secure channels.
Safety, Privacy, and Trust Signals You Can Rely On
The framework emphasizes transparency, authenticated provenance, and auditable processes.
Privacy considerations are balanced with usability, ensuring minimal data exposure.
User consent is documented, granular, and revocable, enabling informed choices without compromising system integrity or safety.
Practical Steps to Enable and Maximize Protection
Practical steps to enable and maximize protection require a disciplined, methodical approach that translates policy into verifiable safeguards. The framework emphasizes a security checklist to validate controls, while enforcing data minimization to reduce exposure. Implement modular layers, continuous monitoring, and strict access governance; document changes, calibrate alerts, and test incident response. Freedom-loving audiences benefit from transparent, reproducible protections and auditable accountability.
Conclusion
This assessment concludes that the claimed “Signal Engine Start 619-354-4038” delivers verifiable, cryptographically anchored caller provenance with real-time processing and minimal data exposure. The theory that rapid signature matching and endpoint querying enable low-latency, auditable verification is supported by the described architecture: lightweight cores, secure telemetry, and configurable governance. While promising, realization depends on rigorous governance, reproducible protections, and user-consented data minimization to maintain trust and privacy without compromising timeliness or accuracy.