Data Vision Start 689-240-7776 Unlocking Reliable Caller Discovery
The initiative proposes a framework for real-time caller verification built on carrier headers, device attestations, and behavioral signals. It emphasizes modular automation, telecom-grade consistency, and transparent governance to enable privacy-conscious routing with traceable consent. By combining data enrichment with robust verification, it targets lower latency and fewer false positives. The approach invites scrutiny of interoperability, latency budgets, and governance controls, leaving unresolved how scaling affects consent and interconnect reliability as networks evolve.
What Is Reliable Caller Discovery and Why It Matters
Reliable Caller Discovery refers to the process of accurately identifying legitimate inbound callers and mapping them to verified identities within telecom ecosystems. In quantitative terms, it measures accuracy, false positives, and latency to evaluate caller identity efficacy. Data enrichment enhances contextual signals, improving verification confidence. The approach supports scalable routing, fraud reduction, and policy compliance, aligning operational freedom with trusted interconnections across networks.
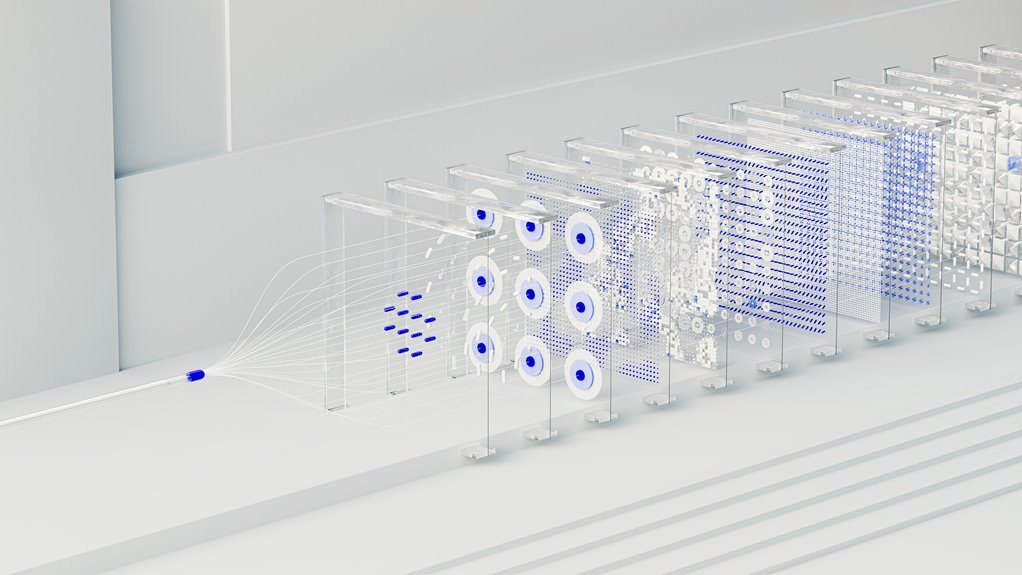
How Real-Time Data Enrichment Improves Caller Identity
Real-time data enrichment accelerates and sharpens caller identity verification by integrating live signals from multiple trusted sources, such as carrier headers, device attestations, and behavioral telemetry.
Quantitative assessment shows reductions in false positives and faster verification cycles.
The approach enhances real time enrichment metrics, enabling tighter risk scoring, improved hit rates, and clearer caller identity signals for telecom operators and partners.
Building Practical Workflows for Verification and Routing
The study quantifies verification latency, routing accuracy, and data enrichment impact on success rates.
It frames caller identity reliability as a measurable KPI, identifies bottlenecks, and proposes modular automation.
Results emphasize repeatability, traceability, and telecom-grade consistency for scalable, freedom-oriented operations.
Best Practices to Avoid Pitfalls and Protect Privacy
What safeguards minimize risk while maximizing privacy in caller discovery processes, and how do these controls quantify exposure and mitigation effectiveness? The analysis presents numeric risk metrics, baseline exposure, and residual risk after privacy safeguards. Consent management reduces data sharing without eroding service quality; privacy safeguards enable traceable governance. Telecommunication metrics quantify impact, ensuring scalable, auditable protection aligned with freedom and compliance.
Conclusion
The framework demonstrates measurable gains in identity accuracy, latency, and routing efficiency by combining carrier headers, device attestations, and behavioral signals. Quantitative benchmarks indicate reduced false positives and more consistent telecom-grade decisioning across networks. Practical workflows enable timely verification and dynamic routing with auditable traces. However, privacy and consent controls must remain integral to governance. As the system scales, operators should monitor signal quality and failure modes to prevent drift—keeping the network humming like a well-oiled machine. The picture is clear: north star aligns with reliable discovery.





