Contact Matrix Start 682 205 8208 Guiding Reliable Caller Lookup

Reliable Caller Lookup combines multi-source verification to determine call origins with verifiable accuracy. It cross-references databases, analyzes metadata, and validates carrier signals to document concordance between presented numbers and authoritative sources. The workflow progresses from initial screening to deliberate whitelisting, applying risk scoring while upholding privacy and auditability. The approach seeks a balance between speed and precision, supporting transparent governance. The implications for legitimate communications are clear, yet gaps and challenges suggest further scrutiny beyond the surface.
What Is Reliable Caller Lookup and Why It Matters
Reliable caller lookup refers to the process of identifying the origin of a phone call with verifiable accuracy, using data from multiple sources to confirm the caller’s identity and location. It emphasizes systematic validation, cross-referencing records, and audit trails. This discipline supports informed decisions, reduces risk, and enhances trust.
Reliable caller and identity verification underpin responsible communication and freedom from deception.
Verifying Numbers: Techniques to Confirm Caller Identities
In the context of confirming caller identities, practitioners systematically apply a set of verification techniques to ensure the number associated with a call matches credible records.
Verification methods encompass cross-referencing databases, analyzing call metadata, and validating carrier signals.
This process supports identity assurance by documenting concordance between presented numbers and authoritative sources, enabling confident differentiation of legitimate versus spoofed communications.
Building a Trusted Lookup Workflow: From Screening to Whitelisting
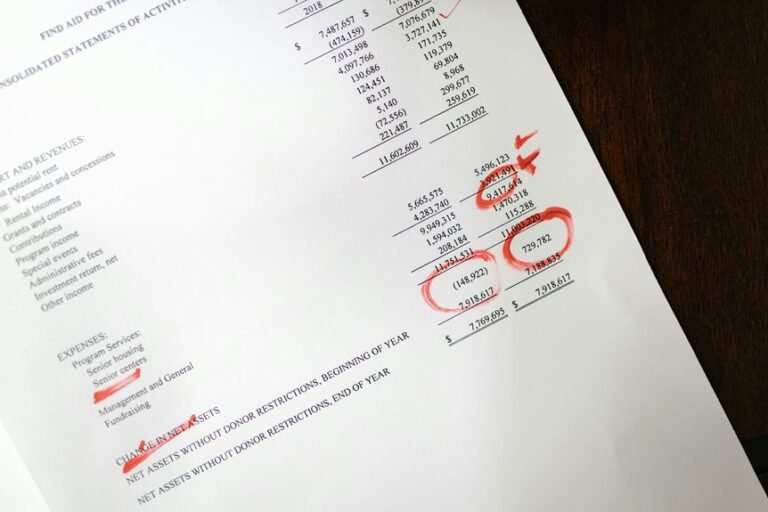
The process of building a trusted lookup workflow moves from initial screening to deliberate whitelisting, establishing a structured sequence that reduces false positives and safeguards caller identity.
The method analyzes caller validation steps, applies risk scoring, and enforces privacy compliance. Clear user consent mechanisms underpin data handling, ensuring governance, traceability, and freedom to opt out within a disciplined, auditable framework.
Privacy, Speed, and Compliance: Balancing Safety With Usability
A balance among privacy, speed, and compliance shapes the effectiveness of caller lookup systems by aligning data practices with performance goals and regulatory requirements. The analysis examines privacy safeguards, ensuring minimal exposure while maintaining traceability.
It evaluates speed optimization strategies, balancing latency against verification accuracy.
Compliance framing informs risk reduction, guiding transparent governance, auditable processes, and accountable data handling for freedom-aware implementations.
Conclusion
In a quiet harbor, a lighthouse keeper cross-checks lanterns against star maps, stubbornly verifying each beacon before lighting the way. The system functions as that keeper: an allegory of deliberate checks, multi-source vitals, and auditable trails. Numbers travel like ships, and the beacon must reflect a true course. Through screening to whitelisting, risk scores become ballast, ensuring safe passages. The voyage remains steady—privacy intact, speed preserved, and trust earned through meticulous, replicable validation.