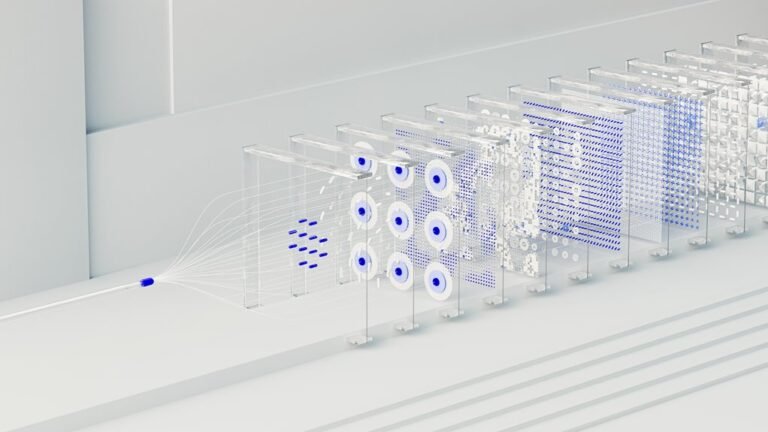
Neural Flow 2015475477 Cyber Node
The Neural Flow 2015475477 Cyber Node integrates neural flow concepts with a cyber node architecture for edge analytics. It emphasizes real-time processing, data minimization, and provenance. The system curates secure, low-latency decision streams across distributed nodes while prioritizing fault tolerance and ethical governance. Its architecture supports scalable, policy-driven orchestration. Yet questions remain about interoperability, resilience under stress, and the balance between autonomy and control as networks evolve.
What Is the Neural Flow 2015475477 Cyber Node?
The Neural Flow 2015475477 Cyber Node represents an integrated computational unit designed to facilitate autonomous data processing, decision-making, and secure communication within a distributed network. It embodies neural flow principles and a cyber node architecture for real time analytics and edge processing, underpinned by security protocols and fault tolerance.
Ethics considerations guide autonomy governance, network orchestration, and scalability planning.
How the Cyber Node Enables Real-Time Analytics at the Edge
Real-time analytics at the edge are enabled by the Cyber Node through a tightly coupled combination of local data processing, streaming inference, and secure, low-latency communication.
The architecture supports edge reasoning by translating sensor streams into actionable models, with continuous adaptation and provenance.
Emphasis on data minimization reduces transmitted payload, preserving bandwidth while maintaining analytic rigor and autonomy.
Security and Resilience: Protocols, Fault Tolerance, and Ethics
Security and resilience in the Cyber Node framework hinge on robust protocols, fault-tolerant design, and ethical governance that accompany real-time analytics at the edge. The analysis evaluates protocol rigor, failure modes, and recovery timelines, emphasizing privacy governance and data provenance as core constraints. Systemic transparency enables independent verification, while principled decentralization supports resilient operations without compromising freedom or accountability.
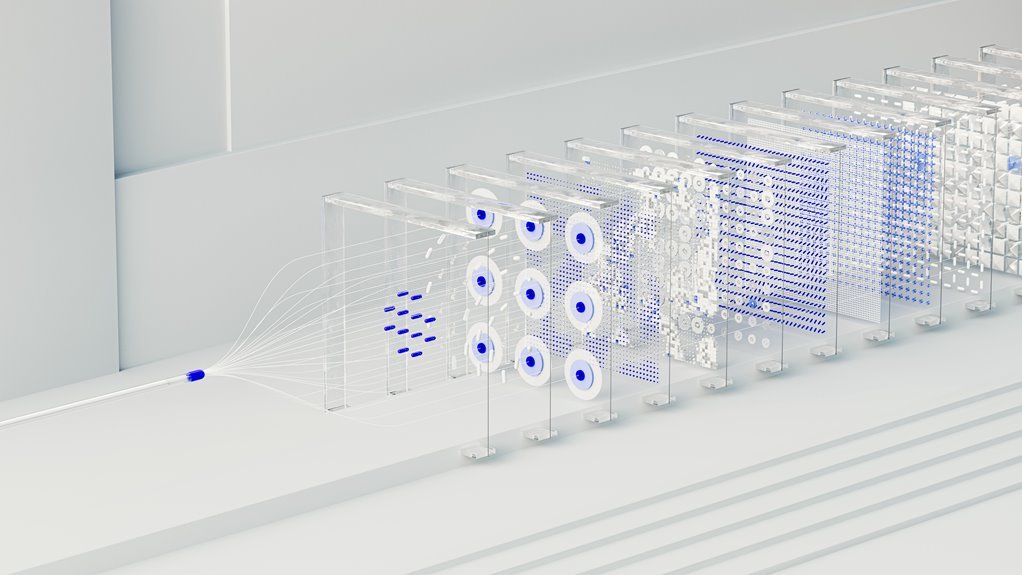
Use Cases Across Networks: Scalability and Autonomous Orchestration
How do networks scale and coordinate autonomously across heterogeneous environments? The analysis maps scalable architectures, edge orchestration, and governance models, emphasizing modularity and policy-driven control. Performance hinges on latency-aware orchestration, distributed state consistency, and real-time telemetry. Scalability analytics quantify throughput and resilience, enabling autonomous adjustments. Patterns emerge: hierarchical control with local autonomy, interoperable protocols, and continuous feedback loops that reinforce reliable cross-network operations.
Conclusion
The Neural Flow 2015475477 Cyber Node represents a measured advancement in edge computing, balancing capability with caution. Its analytic framework, coupled with resilient protocols, yields dependable, real-time insights while maintaining privacy and governance. Through methodical data minimization and provenance practices, operational transparency is enhanced, and risk is gently mitigated. In practice, the architecture supports scalable, autonomous orchestration across networks, enabling nuanced decision-making with a bias toward safety and ethical alignment. Overall, gains accrue with disciplined, incremental implementation.