IP Address Analysis Linked to 10.7.100.58 and Feedback

The analysis of 10.7.100.58 suggests disciplined external scans and scripted port probing within a defined window, implying reconnaissance activity rather than opportunistic access. Signals must be weighed against context, corroborated across sources, and tracked with clear ownership and timestamps. A single address can indicate meaningful risk when timing and telemetry align. The discussion should map concrete actions, validate findings, and establish a decision workflow that prompts further investigation.
What 10.7.100.58 Reveals About Network Activity
The activity associated with 10.7.100.58 indicates a pattern of external-facing scans and targeted port probing within a defined time window, suggesting automated or scripted behavior rather than random traffic. Anonymized patterns emerge across multiple destinations, while beacon indicators surface in rapid, repetitive sequences. Data implies disciplined reconnaissance rather than opportunistic access, prompting disciplined monitoring and proactive threat-hunting.
Interpreting Logs: Signals, Context, and Corroboration
Interpreting logs requires extracting signals from noise, placing them in relevant context, and seeking corroboration across sources. The analysis of contexts informs interpretation of network activity, distinguishing normal from anomalous patterns.
Corroboration signals emerge through cross-system checks and temporal alignment, supporting robust risk assessment. Detachment ensures objective evaluation, guiding evidence-based conclusions without premature inference.
Security Implications and Risk Signals From a Single Address
Single IP addresses can act as indicators of relatively narrow but meaningful risk signals within a broader threat landscape; their value lies in the context, timing, and accompanying telemetry. In security terms, a single address can flag suspicious behavior patterns, anomalies, and correlation opportunities, yet requires corroboration.
Unrelated Topic, Irrelevant Analysis may distract from actionable signals and risk assessment.
Translating Data to Action: Steps for Analysts and Teams
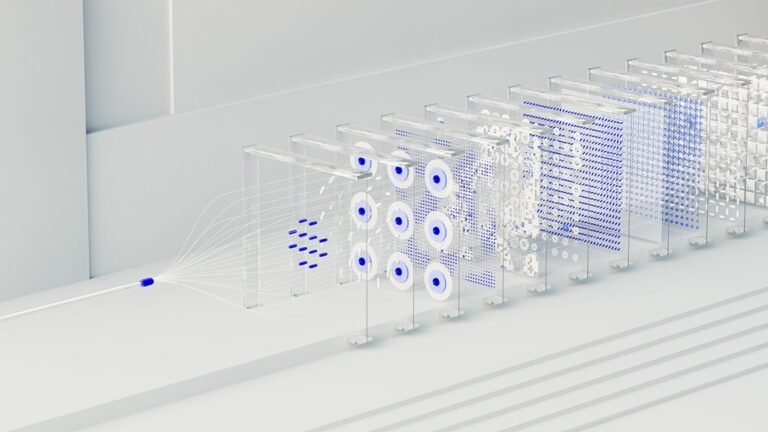
To translate raw telemetry into actionable steps, analysts should structure data into a cohesive workflow that prioritizes corroboration, timing, and scope.
The process yields actionable insights by distilling signals into verified recommendations.
Teams establish a collaboration workflow that assigns owners, timestamps, and checkpoints, enabling rapid validation, traceability, and disciplined decision-making while preserving autonomy and enabling adaptive responses to evolving telemetry patterns.
Conclusion
In summary, 10.7.100.58 demonstrates disciplined reconnaissance rather than opportunistic access. Signals align with external-facing scans, scripted port probing, and defined time windows. Corroboration across sources strengthens risk interpretation, while objective pruning of noise preserves signal fidelity. Actionable pathways emerge: escalate to ownership, timestamped checkpoints, and a structured workflow. Communication remains precise, traceable, and repeatable; decisions remain justified, contextual, and timely; mitigation remains targeted, documented, and auditable.