Signal Guide Start 717-884-0496 Unlocking Phone Discovery Insights

Phone discovery operates as a disciplined sequence of broadcast, listen, and match cycles to reveal devices, networks, and services within reach. It emphasizes reliable data, synchronized timing, and deterministic handshakes to build actionable visibility while preserving user autonomy. The framework aids asset awareness, security posture, and resource planning. Yet, gaps remain where signals falter or privacy constraints complicate mapping, inviting further scrutiny into how such mechanisms can be refined and trusted.
What Is Phone Discovery and Why It Matters
Phone discovery refers to the process of identifying and understanding the devices, networks, and services reachable within a given environment, enabling efficient management and optimization. It clarifies asset scope, informs security posture, and guides resource allocation.
Phone discovery emphasizes repeatable methods, reliable data, and timely updates.
Discovery mechanisms include scanning, protocol negotiation, and inventory integration, delivering actionable visibility while preserving privacy and freedom.
How Signals Find Each Other: The Discovery Process Explained
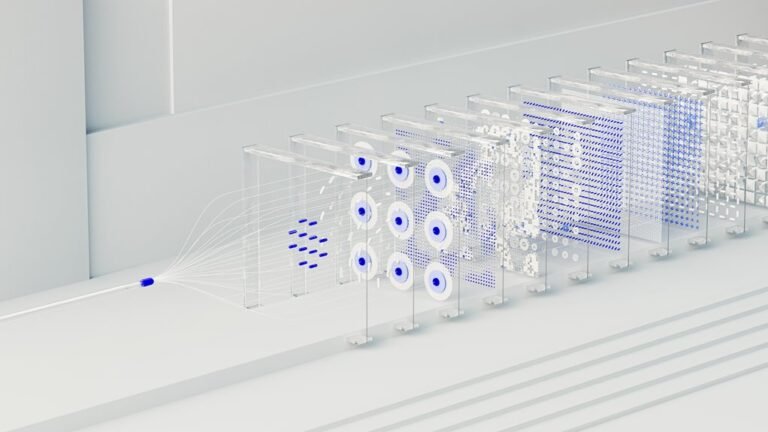
Signal discovery unfolds through a structured sequence that enables entities to locate and identify one another within a networked environment. The discovery process involves broadcasting, listening, and selective matching, where what signals reveal about capability and intent guides alignment.
How signals find partners depends on protocols, timing, and contextual relevance, ensuring efficient connection while preserving autonomy and freedom in diverse networks.
two two-word discussion ideas: bandwidth autonomy. discovery efficiency
Practical Steps to Speed Up Discovery in Real Devices
To accelerate discovery on real devices, a disciplined sequence of practical steps can minimize latency and maximize successful matches.
Practitioners pursue speed optimization through streamlined prompts and tight synchronization, emphasizing consistent device pairing procedures, time-conscious scanning, and deterministic handshakes.
Careful scheduling, minimal interference, and secure channel setup further reinforce rapid results while preserving user autonomy and operational freedom in the discovery workflow.
Troubleshooting Common Discovery Pitfalls and Fixes
Discrepancies and environmental factors often undermine discovery workflows, necessitating a focused troubleshooting orientation after establishing streamlined real-device procedures.
The guide identifies common pitfalls: inconsistent data collection, misconfigured test harnesses, and undocumented latency factors.
Systematic fixes include baseline measurements, synchronized clocks, controlled environments, and incremental validation.
Documentation, repeatable checks, and clear rollback paths ensure resilient troubleshooting without compromising discovery timelines.
Conclusion
In this structured ecosystem, phone discovery hinges on disciplined broadcasting, listening, and selective matching to reveal devices and services within reach. Synchrony, reliability, and privacy-preserving handshakes enable accurate asset visibility and timely updates. A hypothetical enterprise case shows a security team rapidly identifying unauthorized devices on a campus network, enabling swift remediation. Proper timing, deterministic protocols, and clear governance turn scattered signals into actionable insights, reducing risk while preserving user autonomy.