Contact Stream Start 717-205-1303 Revealing Phone Trace Insights
The discussion centers on how a phone trace tied to a contact stream can expose metadata—timing, duration, participants, routing—without revealing content. It examines how signaling interactions generate traces, how route mappings form, and where data are stored for pattern analysis. Privacy risks from metadata convergence and re-identification are weighed against telemetry needs and service functionality. The analysis leaves unresolved questions about safeguards and policy choices, inviting further consideration of practical protections and governance.
What a Phone Trace Reveals About Calls and Texts
A phone trace reveals a structured trail of metadata surrounding calls and texts rather than the content itself. The evidence shows timing, duration, interlocutors, and routing patterns, enabling pattern analysis without verbatim messages. This raises privacy risks and security implications, guiding readers toward practical protections and best practices that preserve autonomy while mitigating exposure to tracing or misuse.
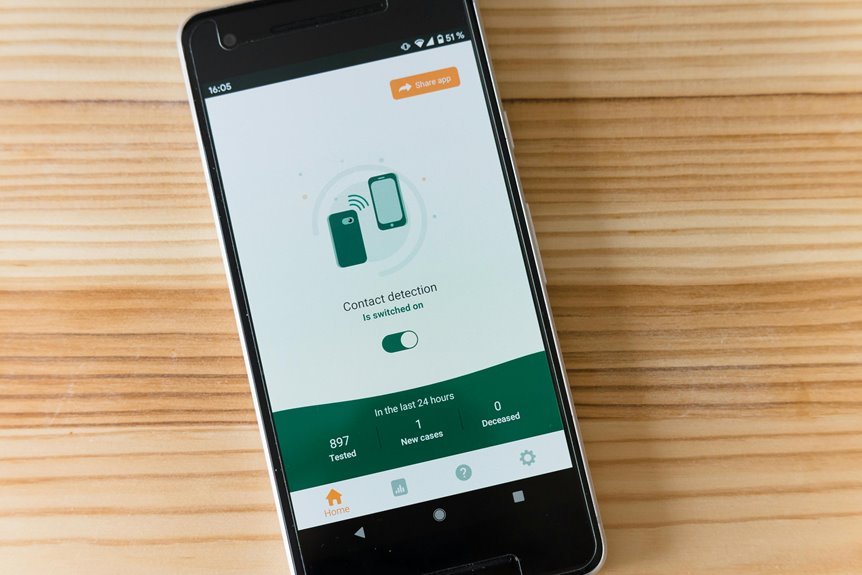
How Contact Stream Traces Are Generated and Collected
Contact stream traces arise from the interactions of signaling protocols, device logging, and network routing that collectively assemble metadata without exposing message content.
The process governs trace generation through labeled events, signaling exchanges, and route mappings, which are subsequently aggregated in centralized stores.
This data collection yields call metadata, contact streams, and related telemetry, enabling analysis while maintaining compartmentalized visibility.
Privacy Risks and Security Implications of Trace Data
Privacy risks associated with trace data arise from the susceptible convergence of metadata, correlation opportunities, and potential exposure of sensitive patterns. The analysis emphasizes privacy implications and the fragility of data provenance, noting how cross-sourced traces can reveal behavioral fingerprints. Security implications include re-identification risks, data leakage, and limited auditability, which undermine trust and strategic autonomy in digital interactions.
Practical Protections and Best Practices for Users
The framework emphasizes minimizing privacy risks, reducing data exposure, and monitoring trace generation patterns, enabling informed decisions, selective sharing, and layered defenses without compromising essential functionality or personal freedom.
Conclusion
In sum, phone traces function as a skeleton key to communication, revealing structure without flesh. The evidence shows signaling patterns, timing, and routing coalescing into a map of activity, enabling pattern analysis while refraining from content. Yet such maps invite re-identification and privacy drift as data converge. Practically, safeguarding requires layered defenses, selective sharing, and minimized exposure. The conclusion: trace data is powerful yet perilous—an analytic beacon demanding disciplined governance and vigilant user-resilience to preserve both insight and anonymity.