Signal Horizon Start 614-758-2377 Unlocking Caller Identity Exploration

Caller identity exploration hinges on tracing signals from TELCO data to device fingerprints, offering a data-driven view of origin and context. The approach aims for transparency, accountability, and privacy safeguards, while handling spoofing risks and regulatory boundaries. It presents practical methods for investigators and researchers, yet the balance between traceability and privacy remains contested. The discussion pauses at a critical decision point: which standards will reliably separate legitimate provenance from deceptive signals, and what consequences follow.
What Is Caller Identity and Why It Matters
Caller identity refers to the information that identifies the origin of a phone call, including the number shown (caller ID) and any metadata transmitted with the call. This construct signs trust and accountability, enabling caller privacy considerations and accountability measures. It informs authentication decisions, where identity verification determines legitimacy, mitigates spoofing risk, and supports informed freedom to communicate while guarding personal data.
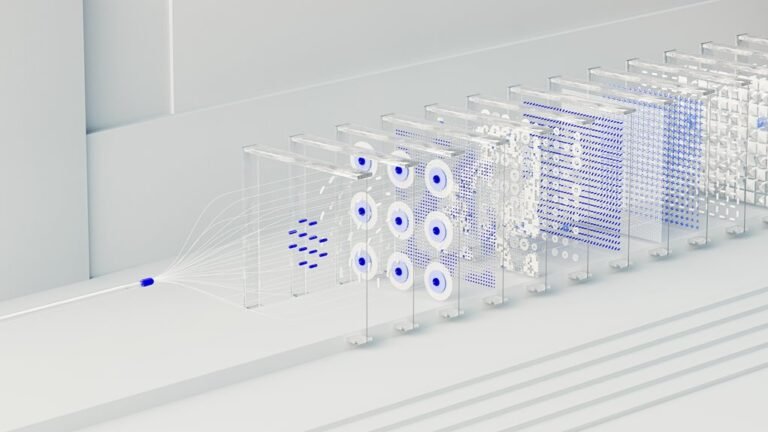
How Modern Tracing Works: From TELCO Data to Digital Footprints
How do modern tracing systems transform raw TELCO data into actionable digital footprints? They mount trace metadata into unified telemetry, extract network provenance, and correlate carrier signals with device fingerprints. The process constructs a transparent trail, enabling contextual timelines and cross-platform links. Results empower freedom-oriented analysis, revealing patterns while preserving interpretive clarity and operational accountability.
Distinguishing Spoofing From Legitimate Tracing: Risks, Rules, and Ethics
This section examines how to differentiate spoofed tracing signals from legitimate, sanctioned tracing, focusing on risk indicators, regulatory constraints, and ethical considerations.
Call tracing data integrity hinges on verifiable sources, audit trails, and timestamp accuracy.
Spoofing risks escalate with weak authentication; ethics guidelines demand transparency, consent, and minimal exposure.
Regulatory compliance shapes methodologies while preserving freedom to investigate responsibly.
Practical Methods for Investigators and Researchers: Tools, Tactics, and Limitations
The section outlines practical methods available to investigators and researchers for tracing signals, validating origins, and assessing reliability in a data-driven, constraint-aware framework.
It emphasizes reproducible workflows, open-source tools, and transparent methodologies while recognizing limits of access, latency, and legality.
Caller privacy, data ethics, and risk assessment shape tool selection, validation criteria, and interpretive rigor within a freedom-oriented analytical culture.
Conclusion
Caller identity tracing sits at the intersection of network provenance and device fingerprints, offering transparent, context-rich timelines while balancing privacy. Data-driven methods—from TELCO signals to digital footprints—can illuminate origins and accountability, yet legwork must guard against spoofing and regulatory risk. Ethical, reproducible practices remain essential. Can investigators consistently separate legitimate traces from manipulated signals, ensuring trust without overreach, as they map cross-platform links and protect user privacy in a complex communications ecosystem?